The Crunchyroll Breach Explained: How a Vendor Login Exposed 6.8M Users
Attackers didn’t breach Crunchyroll’s systems, they logged in through a compromised vendor account. The incident highlights a growing risk: third-party access across SaaS environments.

A few days ago, early reports suggested a potential breach at Crunchyroll linked to a third party, and now we have more clarity.
According to Reuters, Crunchyroll is investigating a breach after attackers claimed to have accessed data belonging to nearly 6.8 million users.
The entry point wasn’t Crunchyroll’s infrastructure. It was a support agent.
What actually happened
Based on reporting from BleepingComputer, attackers allegedly gained access to an Okta SSO account belonging to a customer support agent working for TELUS International.
The method is familiar.
Malware on the agent’s device → credentials stolen → access reused across systems.
Zendesk. Google Workspace. Jira. Slack. No exploit. No brute force. Just logging in.
Within ~24 hours, attackers claim they extracted millions of records, including emails, IP addresses, and support ticket data.
This is the pattern, not the exception
If this feels familiar, it should.
- Jaguar Land Rover. Breached through a third-party contractor account
- Qantas. Supplier access used to reach internal systems
- Marks & Spencer. Third-party exposure leading to operational disruption
Different industries. Same entry point. Trusted access that no one was really watching.
Hackers don’t hack in. They log in.
What these incidents show is a shift most teams still underestimate. Attackers don’t need to break your controls if they can use them.
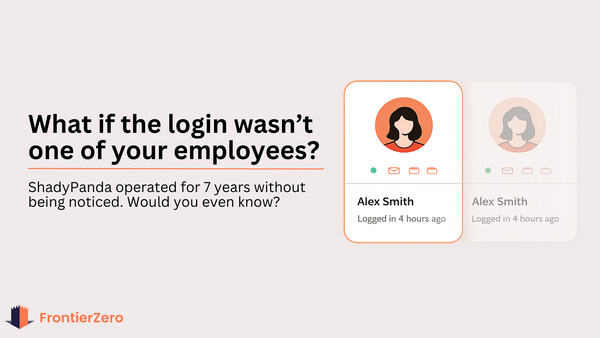
A valid login, especially through SSO, often looks completely normal. And when that identity belongs to a vendor or contractor? It’s even harder to question.
The real risk sits outside your organisation
Most security strategies are still built around employees and devices. But your environment now includes:
- outsourced teams
- partners
- service providers
- integrations across dozens of SaaS apps
Each one introduces identities you don’t fully control. And in many cases, you don’t fully see.
The scenarios that matter
- What happens if a vendor employee hasn’t logged in for months, but still has access?
- What happens when they leave their company?
- What happens if their credentials are exposed through malware or another breach?
You won’t see an “attack.” You’ll see a normal login until it’s too late.
You can be breached without being breached
You can be breached without being breached
Crunchyroll may still be investigating, but the takeaway is already clear.
You don’t need to be directly compromised to lose data. You just need someone in your supply chain to be.
And when that happens, the impact lands with you:
your users
your data
your reputation
What this means for security teams
Modern environments extend far beyond internal systems.
They include vendors, contractors, support teams, and integrations across dozens of SaaS platforms. Each introduces identities and access paths that often sit outside traditional visibility.
Most teams can confidently answer: “What’s happening inside our environment?”
Far fewer can answer: “What’s happening across the identities connected to it?”
That’s where these breaches start.
Solutions like FrontierZero focus on mapping and monitoring those external identities and connections across SaaS environments. By tracking how access behaves over time, security teams can detect when something deviates, before it becomes a breach disclosure.
Understanding who has access, and how that access is used, is becoming a core requirement for modern security.
If you want to understand what your external exposure actually looks like, you can request a demonstration below.
See all the people who have access to your systems in 15 minutes.