Lazarus Ransomware Attacks in the Middle East: What It Means
A recent campaign linked to North Korea’s Lazarus Group targeted organizations in the Middle East using Medusa ransomware. The attack highlights how modern ransomware operations work—and why identity and SaaS visibility are becoming critical for security teams.

Researchers confirmed last month that the Lazarus Group (North Korea's most capable state-sponsored hacking unit) used Medusa ransomware in a direct attack against an organization in the Middle East. A second attack targeted a U.S. healthcare provider. Both were part of the same campaign.
This is not background noise. This is a named region, named victims, and a named threat actor operating with nation-state resources.
The rise of Ransomware-as-a-Service changes who can attack you
For years, the assumption was that sophisticated attacks came from sophisticated actors. Nation-states ran advanced campaigns. Criminal gangs ran mid-tier operations. The level of threat you faced correlated roughly with how interesting a target you were.
That assumption no longer holds.
Lazarus didn't build Medusa. They rented it. Operating as an affiliate of a criminal RaaS operation called Spearwing, which has now claimed over 366 attacks globally. Other North Korean groups have done the same, pivoting from custom-built malware to off-the-shelf ransomware from Qilin and Play. The motivation, as Symantec put it, is pragmatism. Why invest in building your own tooling when proven infrastructure is available for a cut of the ransom?
The consequence is significant. RaaS has industrialized attack capability. What once required a nation-state budget now requires a subscription. The barrier to running a sophisticated ransomware campaign has collapsed, and the number of actors capable of running one has multiplied.
For organizations in the Gulf, this matters in a specific way. The region is one of the fastest-growing digital economies in the world. High-value targets, rapid SaaS adoption, complex vendor ecosystems, and, in many cases, security programs are still catching up to the pace of growth. That combination is exactly what RaaS affiliates look for.
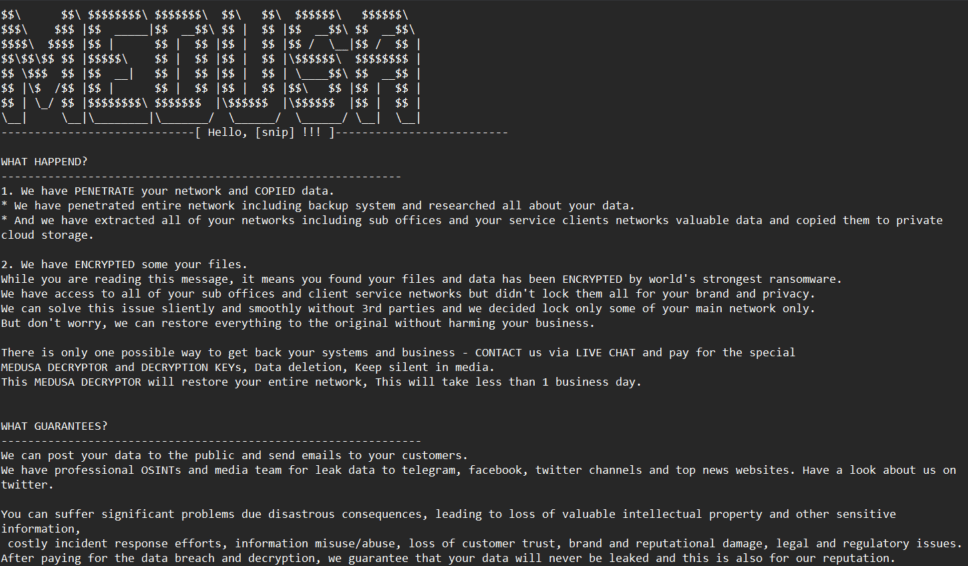
The attack doesn't start with ransomware

The Lazarus campaign toolkit tells you everything about how these attacks actually unfold. Before any encryption happened, the attackers were running ChromeStealer to pull passwords from browsers, Mimikatz to dump credentials from memory, and custom backdoors to establish quiet persistence. Ransomware is the last step. By the time systems go dark, the attacker has typically been inside the environment for days or weeks.
This matters because most security programs are oriented around the wrong moment. They are well-equipped to respond to the explosion. They are far less equipped to detect the slow, quiet work that happens before it.
The part most teams aren't watching
Once credentials are harvested, the attacker's next question is simple: what do these keys unlock?
In most organizations today, the answer is a lot more than anyone has mapped. The same identity your staff uses for their primary systems also unlocks the CRM connected via OAuth, the finance tool pulling data through an API, the vendor portal a partner has accessed for two years, and the SaaS platform a team adopted without central approval. Vendor accounts that have access to the company apps. Each of those is a door. Most of them sit outside the visibility of your core security stack.
This is where attacks propagate quietly. Not through your firewall. Through a trusted integration that no one has reviewed recently. Through a vendor account with permissions it no longer needs. Through a service account whose credentials appeared in a dark web dump three weeks ago, and no one was alerted.
The question is not whether something abnormal happens in your environment. Something abnormal will happen. The question is whether you will know about it when it does, and whether you will know about it across all the places your identities live, not just the platforms you watch closely.
Most teams, honestly, cannot answer yes to that. Not because they are careless. Because the tools they have were not built to see that surface.
What visibility actually looks like
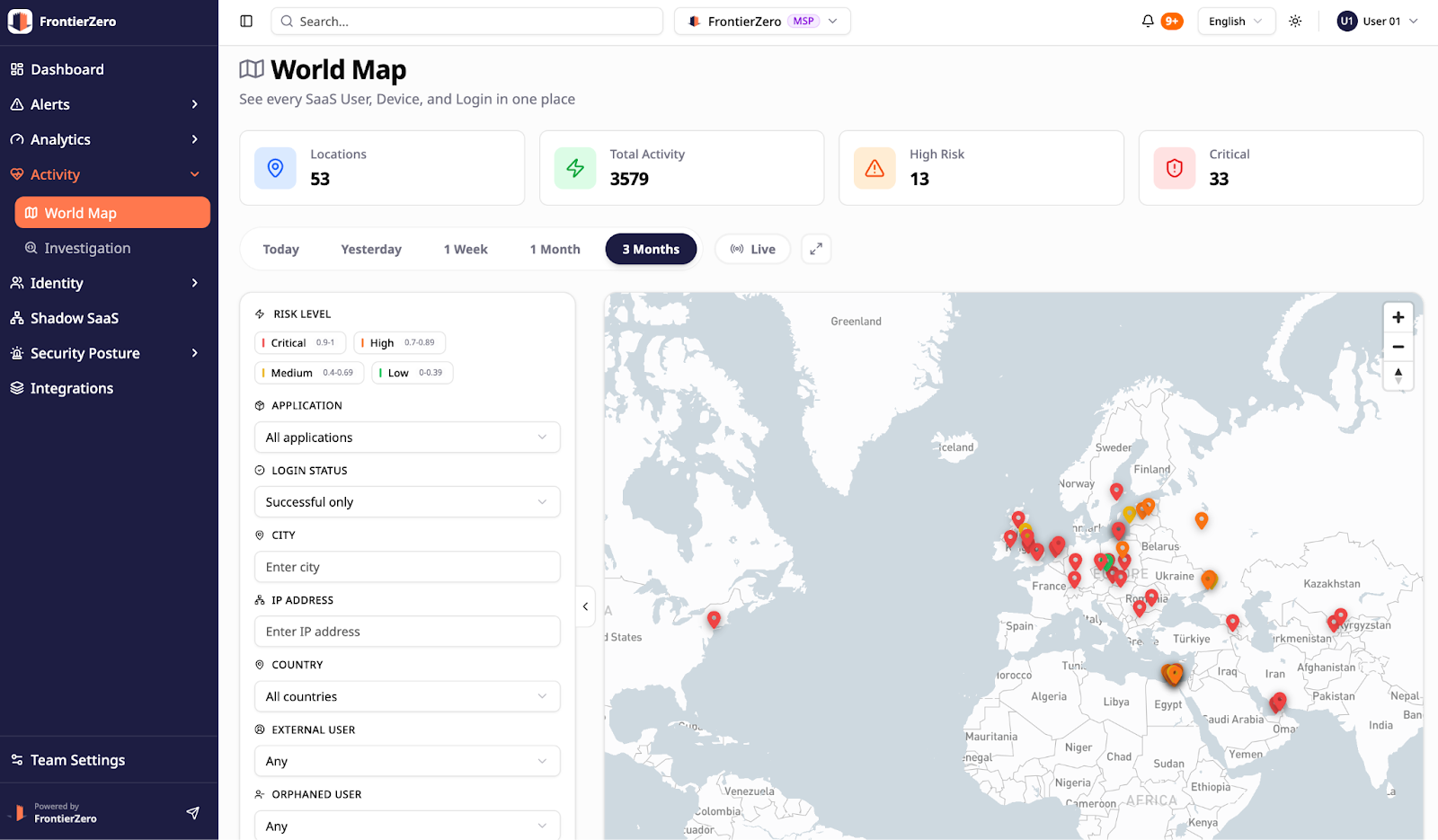
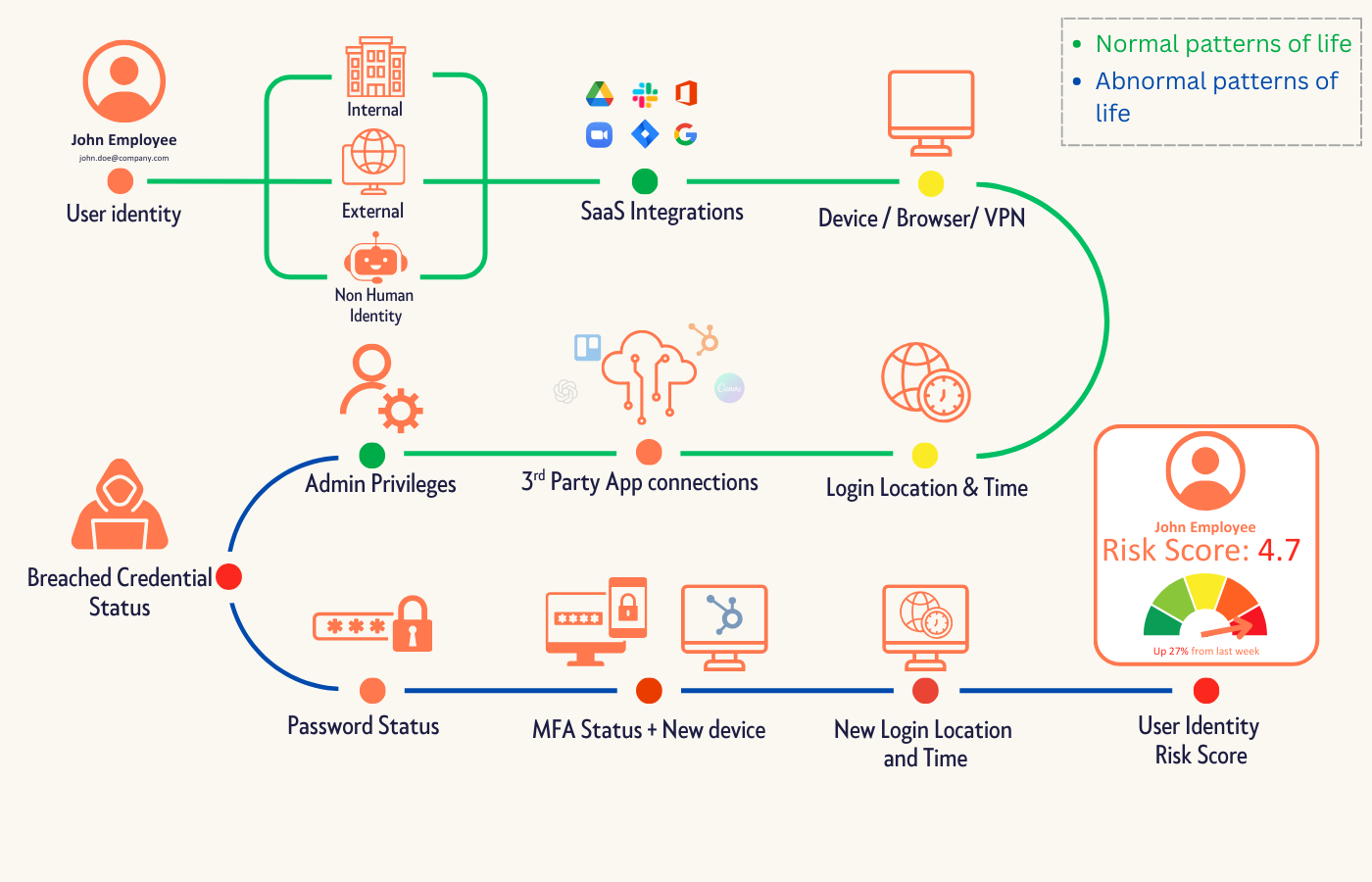
Knowing when something abnormal happens means understanding what normal looks like across your environment.
That includes your core systems, but also the external integrations, SaaS platforms, vendor accounts, and APIs connected to them.
Organizations need visibility into:
- Which third-party tools are connected to their environment
- What level of access do those integrations actually have
- When vendor accounts authenticate outside their normal behavior patterns
- When credentials tied to the organization appear on the dark web
- When integrations begin behaving differently than expected
Without that visibility, abnormal behavior can persist quietly for days or weeks.
This is the exact gap many attackers rely on.
Platforms like FrontierZero focus on mapping these identity connections across the full SaaS ecosystem, monitoring how identities and integrations behave over time, and alerting security teams when something deviates from that baseline.
If you want to understand what your SaaS environment actually looks like today, you can request a demo here.