The Vendor You Trusted Just Exposed 25 Million People
A breach at Conduent exposed the data of 25 million Americans after attackers remained inside the vendor’s systems for three months.

In January 2025, Conduent Business Services discovered attackers had been inside their network for three months.
Not three days. Three months.
By the time anyone noticed, the SafePay ransomware group had already walked out with an estimated 8.5 terabytes of data: Social Security numbers, medical records, health insurance details, government benefits information.
As of February 2026, 25 million Americans have been confirmed affected. 15.4 million in Texas alone.
And here's the part that matters most for your organization:
Conduent's clients had no idea it was happening.
This Is the Same Story, Different Vendor
If you've been following JLR. If you've seen what happened at Nissan.
You already know this pattern.
JLR: compromised through external access.
Nissan: exposed through a third-party Red Hat environment they didn't own, didn't monitor, and couldn't see.
Conduent: attackers inside for 90 days while government agencies and healthcare programs continued sending their most sensitive citizen data through the pipe.
Different vendor. Different sector. Different country.
Same failure.
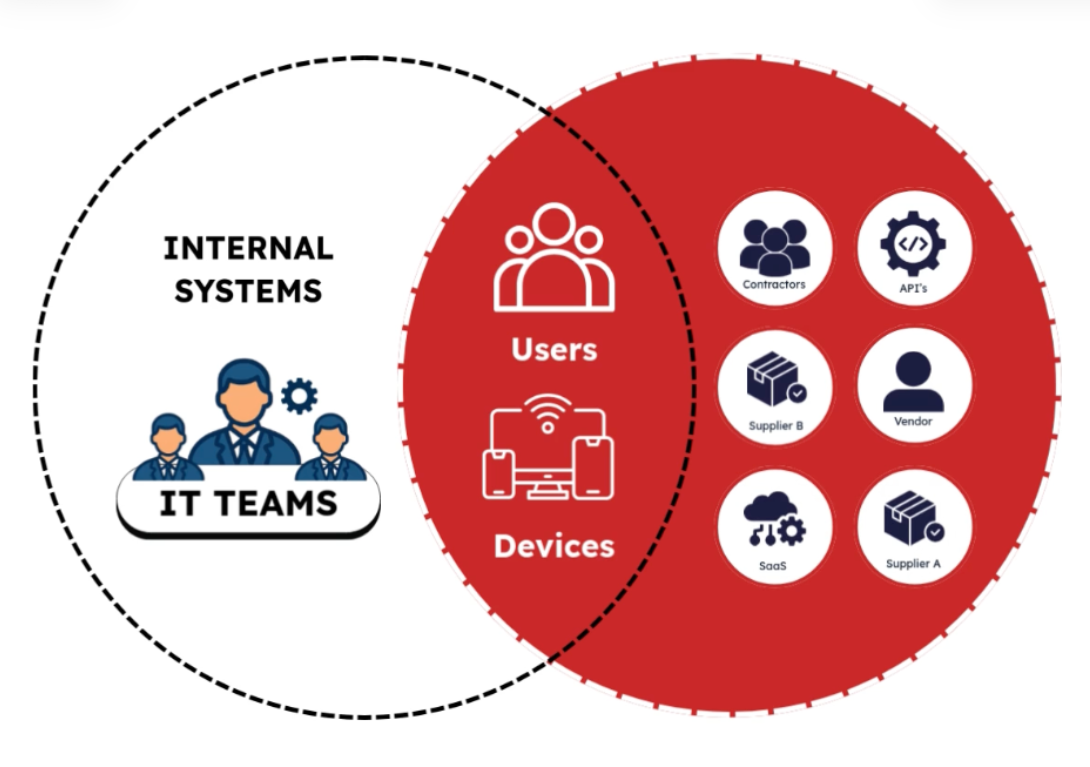
The perimeter didn't break. The connected ecosystem did.
What Conduent's Clients Actually Controlled

Conduent processes Medicaid, public benefits, and government healthcare data for over 100 million U.S. residents. Their clients, which include state agencies, healthcare programs, and government departments, almost certainly had security controls in place.
Firewalls. Endpoint protection. Identity tools. SIEMs.
None of it mattered because the breach didn't happen inside their environment.
It happened inside their vendor's.
And their vendor's environment:
- Was not owned by them
- Was not monitored by them
- Was not visible to them in real time
So they only learned about the exposure after Conduent disclosed it. Not when attackers entered. Not when the data was taken.
After.
That delay is the real risk.
Why This Keeps Happening
Most security teams can answer: "What's happening inside our environment?"
Very few can answer: "What's happening inside the environments that have access to us?"
Which vendors currently have OAuth tokens into your systems? Which SaaS platforms can pull customer data? Which integrations went live last year and were never reviewed? Which contractor credentials are sitting on the dark web right now?
Conduent's clients didn't see it.
And that's exactly why attackers never had to touch their networks.
The Timeline That Should Concern Every CISO in the Region
- October 2024 — Attackers gain access
- January 2025 — Conduent detects the breach
- April 2025 — SEC disclosure
- October 2025 — Victim notifications begin
- February 2026 — 25 million confirmed affected
From breach to victim notification: over a year.
Industry average dwell time is approximately 11 months. Conduent was, in a grim sense, about average.
This is not an American problem. The Gulf region has one of the fastest SaaS adoption curves in the world. Vision 2030, Smart Dubai, digital government initiatives across the UAE and KSA, all of it is accelerating the vendor ecosystem. Every hospital runs third-party claims management. Every government agency is outsourcing benefits processing. Every enterprise with an ERP connected to a procurement platform.
Each connection is a trust relationship. Each trust relationship is an attack surface.
The question isn't whether a Conduent-style breach can happen here. It's: which of your vendors is your Conduent?
What FrontierZero Actually Does
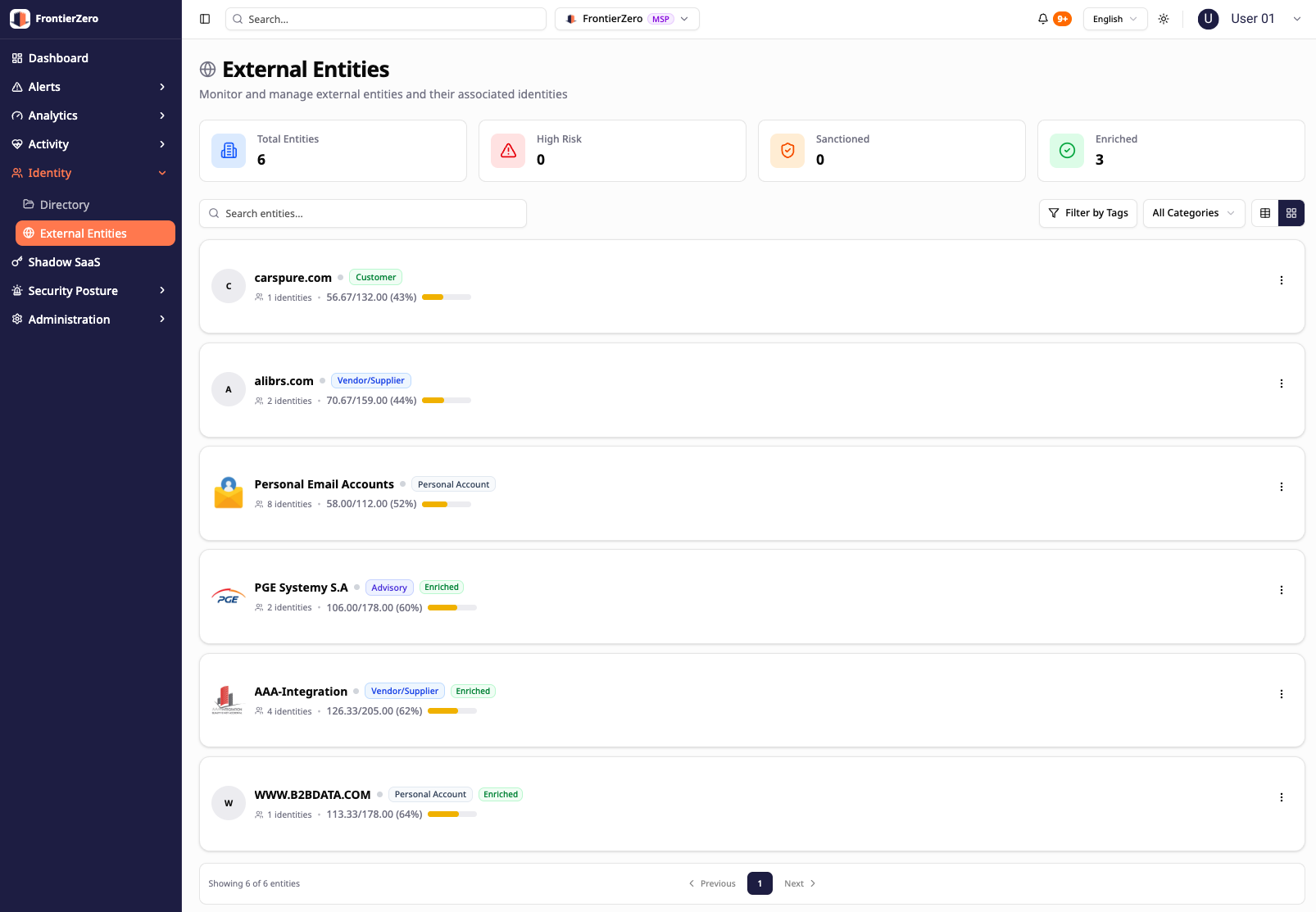
frontierZero wasn't built to solve one narrow problem.
It was built to solve this one: you cannot defend what you cannot see.
We map and continuously monitor:
- External SaaS connections and vendor integrations
- APIs, tokens, and service accounts
- Unapproved and shadow applications
- Vendor and contractor credentials on the dark web
- Data flows across your supply chain
Then we apply pattern-of-life on top of all of it.
So when something changes: a vendor starts pulling unusual volumes of data, a connection behaves outside its normal pattern, an integration that's been quiet for months suddenly becomes active at 2 am from an unexpected location, you don't wait for a breach report.
You see it happen.
In the session. Not after.
See Your Own External Exposure
We built a 2-minute explainer showing exactly how third-party breaches happen, and at the bottom, you can request a free external connections report for your environment.
It shows which third parties have access to your data, what they're connected to, and where your hidden risk actually lives.
Watch it here https://frontierzero.io/supply-chain-video/