The Side Door Problem: What the HackerOne Breach Tells Us About Third-Party Risk
HackerOne wasn’t breached directly. A supplier was. One vulnerability exposed millions across multiple organisations. This is how modern attacks really happen, and why most companies still don’t see the risk.

If there's one breach that should make every security leader pause this quarter, it's this one.
HackerOne, the bug bounty platform that organisations hire specifically to find vulnerabilities in their systems, was caught out by a vulnerability in someone else's system. Not their firewall. Not their code. Not their infrastructure. A third-party employee benefits provider called Navia Benefit Solutions, quietly handling HR data in the background, became the entry point for an attack that exposed the personal information of nearly 300 HackerOne employees.
The irony is almost too neat. A company whose entire value proposition is finding security weaknesses before attackers do, is undone by a supplier they had no reason to distrust.
What happened

An attacker exploited a Broken Object Level Authorization (BOLA) flaw in Navia's environment. A type of vulnerability where an application fails to properly verify whether a user should have access to a specific piece of data, allowing them to pull records they were never supposed to see.
The unauthorised access ran from December 22, 2025, to January 15, 2026. Over those three weeks, the attacker had access to a significant volume of sensitive employee data: Social Security numbers, full names, home addresses, dates of birth, health plan participation details, and information about employees' dependents. The kind of data that doesn't expire. The kind that can be used for identity fraud, phishing, financial theft, or sold on.
Navia detected suspicious activity on January 23. HackerOne received formal notification in March, after letters dated February 20 reportedly got delayed in transit. By the time HackerOne knew what had happened, the window of exposure had been open for the better part of three months.
The Navia breach, it later emerged, wasn't limited to HackerOne. More than 2.6 million people across multiple client organisations were affected. One vulnerability, one supplier, millions of downstream victims, none of whom had any direct relationship with Navia, and none of whom had any way of knowing their data was at risk.
This isn't a one-off

The HackerOne and Navia incident follows a pattern that has become almost routine in enterprise security, and one worth understanding in detail, because it keeps happening to organisations that are doing everything else right.
2025 was particularly brutal for third-party and supply chain risk. Three incidents stand out.
In April 2025, Marks & Spencer was hit by a ransomware attack that paralysed its operations for weeks. The breach was initially thought to be a technical error, but was later revealed to stem from a vendor compromise. Attackers tricked a third-party provider into resetting an internal user's credentials, no firewall bypass, no zero-day exploit. Just a phone call to the wrong person, and a door that opened from the inside. M&S lost roughly £300 million in operating profit and was forced to suspend online orders for 46 days. More than £700 million was wiped from its market value. The same group then went on to target Co-op and Harrods using near-identical methods.
In August 2025, Jaguar Land Rover, suffered what has been described as the most financially damaging cyberattack in British history. The March precursor to the September attack was enabled by credentials stolen from a third-party contractor with access to JLR's Jira system. An employee at a supply chain partner whose login details had been harvested via infostealer malware. The subsequent September attack brought production lines at all three UK plants to a complete halt for three weeks, with an estimated financial impact of £1.9 billion to the UK economy. The attackers didn't need to penetrate JLR's perimeter directly. They came in through a supplier account that was sitting quietly in the background, connected and trusted.
And then, just weeks ago, a Sony subsidiary, Crunchyroll. The breach occurred on March 12, 2026, after a threat actor gained access to the Okta SSO account of a support agent working for Telus International, a business process outsourcing company with access to Crunchyroll's support systems. Around 6.8 million users had data exposed from the company's Zendesk support system, including names, email addresses, IP addresses, and the contents of support tickets. The attackers reportedly issued a $5 million extortion demand. Crunchyroll did not respond. One outsourced employee. One compromised login. Millions of users caught in the middle.
The thread connecting all of these incidents is the same: the breach didn't start inside the victim's environment. It started in a supplier's system, a shared platform, or a third-party tool, and travelled inward from there.
Why this keeps happening, and why it's not IT's fault
It would be easy to look at a breach like HackerOne's and ask why the security team didn't catch it earlier. But that framing misunderstands the nature of the problem.
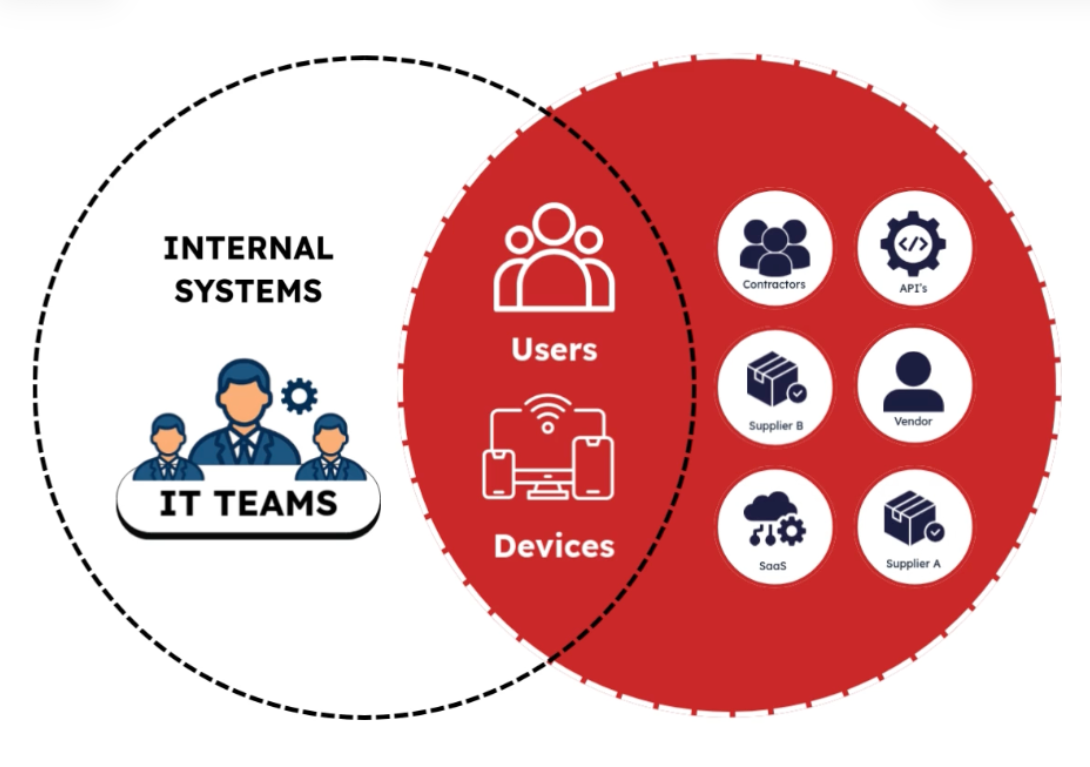
Modern organisations run on SaaS. The average enterprise now uses hundreds of cloud applications: HR platforms, payroll systems, benefits administrators, CRM tools, marketing software, finance integrations, e-signature services, recruitment platforms, and dozens more. Many of these are adopted at the department level, without a formal procurement process. A finance team signs up for an expense management tool. An HR manager connects with a benefits provider. A sales team integrates a new outreach platform. Each decision is reasonable in isolation. Each one creates a new external connection.
Security and IT teams are not always in the room when these decisions are made. And even when they are, the ongoing monitoring of every third-party connection (tracking what access each vendor holds, whether that access is still current, and what the vendor's own security posture looks like) is an enormous operational challenge. There is no malice in the visibility gap. There is no negligence. There is simply the reality of how modern organisations operate, and the pace at which the SaaS environment evolves.
The result is that most organisations have a significant number of active external connections that aren't fully documented, aren't actively monitored, and whose risk profile isn't well understood. Not because anyone made a bad decision, but because the tools to maintain that visibility comprehensively haven't always been in place.
What good looks like
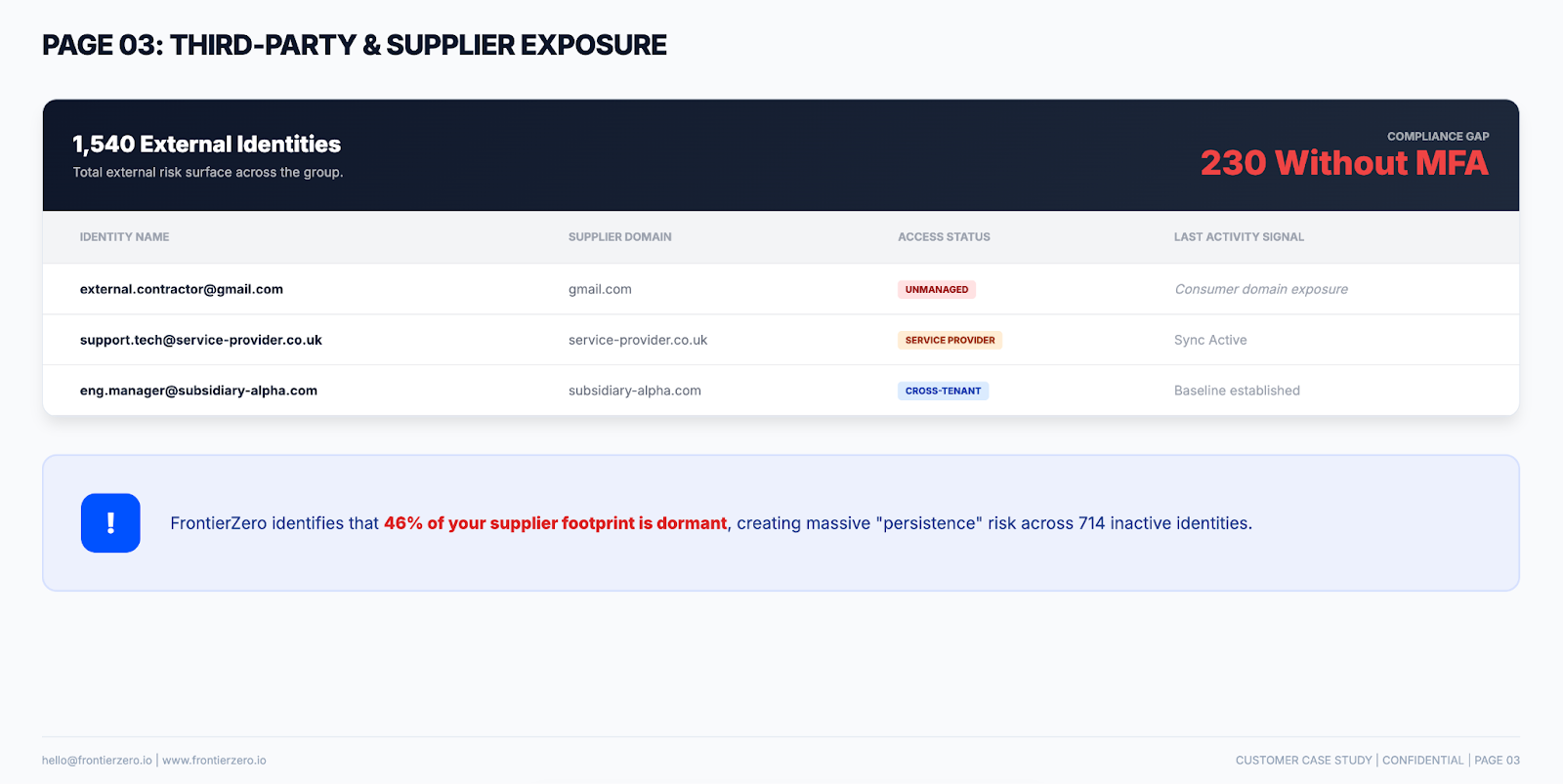
The minimum standard for managing third-party risk has to start with knowing what's connected. Not based on a procurement register from eighteen months ago, but right now, with current data, in real time.
That means continuous visibility into which SaaS applications have active connections to your environment, what level of access each vendor holds, whether those connections are still necessary, and what the risk profile of each supplier looks like. It means being able to answer, within minutes, a question that should be straightforward but rarely is: if one of our suppliers was breached tonight, which of them could cause us a problem, and how serious would it be?
The organisations that can answer that question are in a materially better position, not because breaches don't happen to them, but because they can respond faster, contain the damage more effectively, and make informed decisions about which vendor relationships carry unacceptable risk before something goes wrong.
The HackerOne story is a useful reminder that no organisation is immune. If a company whose entire business is built around finding security vulnerabilities can be exposed through a third-party integration, the assumption that strong internal security controls are sufficient on their own doesn't hold up.
At FrontierZero, we give security teams the visibility they need over their external SaaS connections by mapping every third-party integration active in your environment, with risk context attached, so you know what's connected, who has access, and where the exposure is.
We're offering a Free External Connections Report to get you started. It takes minutes to set up, requires no agents, and gives you a clear picture of your third-party SaaS exposure.
If the HackerOne story made you wonder what's quietly connected to your environment right now, that's probably reason enough to find out.