SaaS Security
The Third-Party Breach List Keeps Growing. Vimeo is the latest to join.
Vimeo was breached through Anodot, a third-party analytics tool. So was Rockstar Games. Same vendor, same month. This is no longer a pattern. It's the playbook.
SaaS Security
Vimeo was breached through Anodot, a third-party analytics tool. So was Rockstar Games. Same vendor, same month. This is no longer a pattern. It's the playbook.

Third-party
HackerOne wasn’t breached directly. A supplier was. One vulnerability exposed millions across multiple organisations. This is how modern attacks really happen, and why most companies still don’t see the risk.

SaaS Security
A recent campaign linked to North Korea’s Lazarus Group targeted organizations in the Middle East using Medusa ransomware. The attack highlights how modern ransomware operations work—and why identity and SaaS visibility are becoming critical for security teams.
SaaS Security
Microsoft gives strong identity visibility, but only inside Microsoft. This explains where today’s SaaS attacks actually start.
Cybersecurity
In December, Nissan lost customer data — even though its own systems weren’t hacked. The problem came from an external platform with standing access. Read how this happened, why it keeps repeating, and what security teams should change.

SaaS Security
Most breaches slip through not for lack of alerts, but for lack of context. Context-based security brings clarity to chaos — helping teams focus on what’s real.

Cybersecurity
Jaguar Land Rover lost millions when one contractor account went unchecked. This wasn’t a system failure; it was a visibility failure. Here’s what every CISO can learn about identity risk and supply chain trust.
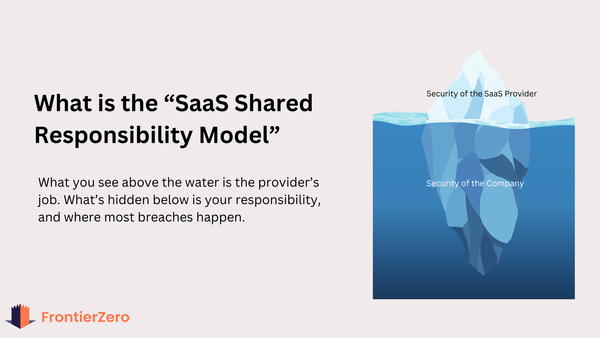
SaaS Security
SaaS providers secure the platform. You’re responsible for everything inside it: users, vendors, permissions, and risk. This blog breaks down where responsibility lies, what’s commonly missed, and how CISOs can prevent the most common SaaS breaches.

Boardroom
Insights from the 2025 IBM Cost of a Data Breach Report
MFA
MFA gaps aren’t just an IT problem—they’re a boardroom risk. Learn how to spot exposed users, admins, and apps in minutes, not months.

SSPM
SaaS tools are the new business layer—but they’ve created a visibility gap security teams can’t ignore. This guide explains what SSPM is, why it matters, and how FrontierZero brings identity and context together to reduce risk where it matters most.
ITDR
SaaS has changed the identity perimeter. In this guide, we break down what ITDR means, why legacy tools miss SaaS threats, and how to catch ghost access.