The Third-Party Breach List Keeps Growing. Vimeo is the latest to join.
Vimeo was breached through Anodot, a third-party analytics tool. So was Rockstar Games. Same vendor, same month. This is no longer a pattern. It's the playbook.
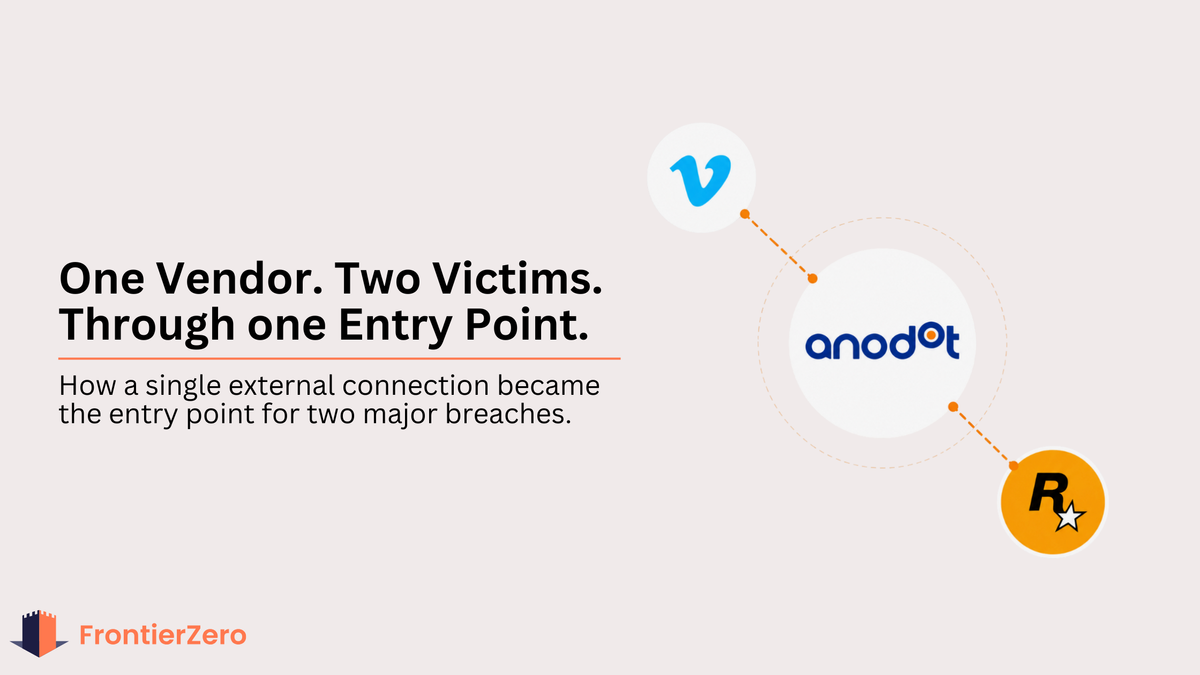
Last week, Vimeo confirmed a breach. Not through a vulnerability in their own systems. Not through a phishing email. Through Anodot, a third-party analytics platform connected to their cloud infrastructure.
Attackers compromised it. And walked straight in.
One integration. Snowflake and BigQuery exposed. Email addresses, metadata, technical data gone. The breach was claimed by ShinyHunters, who set a ransom deadline and threatened to publish everything.
No alarm triggered. No perimeter crossed. Just a connected tool nobody in security was watching, and a door that had been open longer than anyone knew.
Vimeo did nothing wrong. That is exactly the problem.
Same vendor. Different victim. Same month.

Rockstar Games went down through Anodot too. Same vendor, same group, same month. Attackers walked into their Snowflake environment through a cloud monitoring tool with standing access and left with 78.6 million records. Zero alerts. The access looked completely legitimate because it was. We broke down the full Rockstar story here.
And before Anodot, there was Crunchyroll. 6.8 million users exposed through a compromised vendor login. Attackers did not touch Crunchyroll's systems. They logged into them through a third-party outsourced support company with valid credentials. No forced entry. No technical exploit. Just a vendor account that nobody was monitoring. Full breakdown here.
Then HackerOne. A third-party benefits provider had been sitting unmonitored inside their environment for weeks before anyone noticed. One supplier with legitimate access. One blind spot. The full story is here.
And Vercel. Breached through Context.ai, an AI tool one of their employees was using, with OAuth access to Google Workspace. When attackers compromised the tool, they inherited the session. They moved laterally into Vercel's internal environments and accessed API keys, database credentials, and authentication tokens. Quietly. Without triggering a single alert. We covered what this means for Shadow AI risk here.
The pattern is always the same. Attackers are not breaking through walls. They are finding the vendor that already has the keys.
Last year made this impossible to ignore

If 2026 feels relentless, 2025 was where the pattern became undeniable.
JLR, Qantas, and Workday were among the names that resonated most with the security leaders we spoke to. Household names. Significant security investments. All compromised through external connections rather than direct attacks.
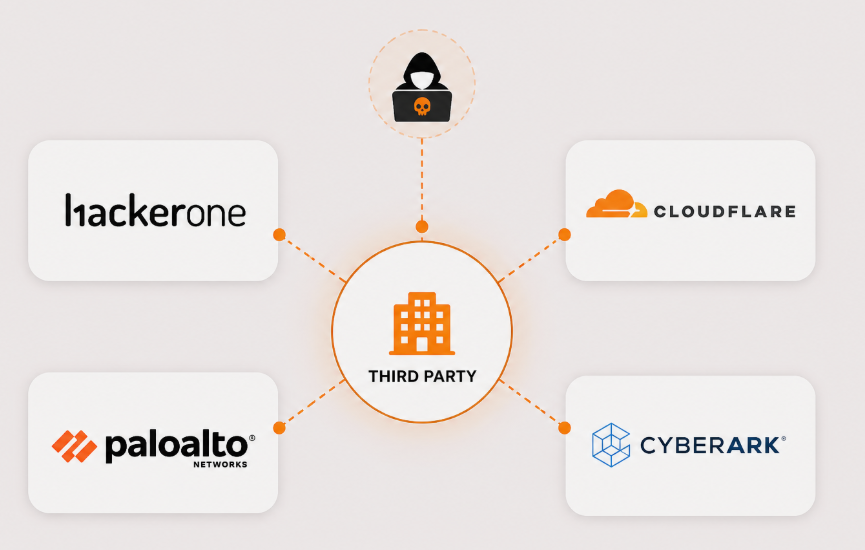
And they were not alone. Marriott, Hilton, Hyatt, and Wyndham were all breached through the same hotel management software simultaneously. 94 schools across the United States lost student Social Security numbers and medical records through a single cloud provider. Cloudflare, Palo Alto Networks, CyberArk, Zscaler, and HackerOne all shared the same blind spot through a single chatbot provider. Cisco, Air France-KLM, TransUnion, Pandora, and Chanel all hit through Salesforce in the same window. OpenAI exposed through a product analytics tool.
The full list from 2025 includes: JLR, Qantas, Workday, Marriott, Hilton, Hyatt, Wyndham, Cloudflare, Palo Alto Networks, CyberArk, Zscaler, Cisco, Air France-KLM, TransUnion, Pandora, Chanel, Farmers Insurance, OpenAI, SoundCloud, Grubhub, Canada Goose, Ericsson, and dozens more.
One external connection compromised. Multiple victims every time.
2026 is following the same trajectory. Rockstar, Crunchyroll, Vercel, HackerOne, and now Vimeo. The table below shows the pattern continuing.
If it happens to them, it happens to you
Here is what most security conversations miss.
When HackerOne, Cloudflare, Palo Alto Networks, and CyberArk, companies whose entire business is security, all share the same third-party blind spot, the assumption that mid-market organizations have better visibility is not realistic. It is wishful thinking.
And attackers know it. A compromised vendor serving fifty mid-size enterprises is just as valuable as one serving a single enterprise. The data volume is comparable. The detection risk is lower. Mid-size organizations are increasingly targeted not despite being smaller, but because their third-party exposure is just as wide and their visibility is significantly narrower.
You do not need to be the primary target to become the primary victim.
Why nobody sees it until it is too late
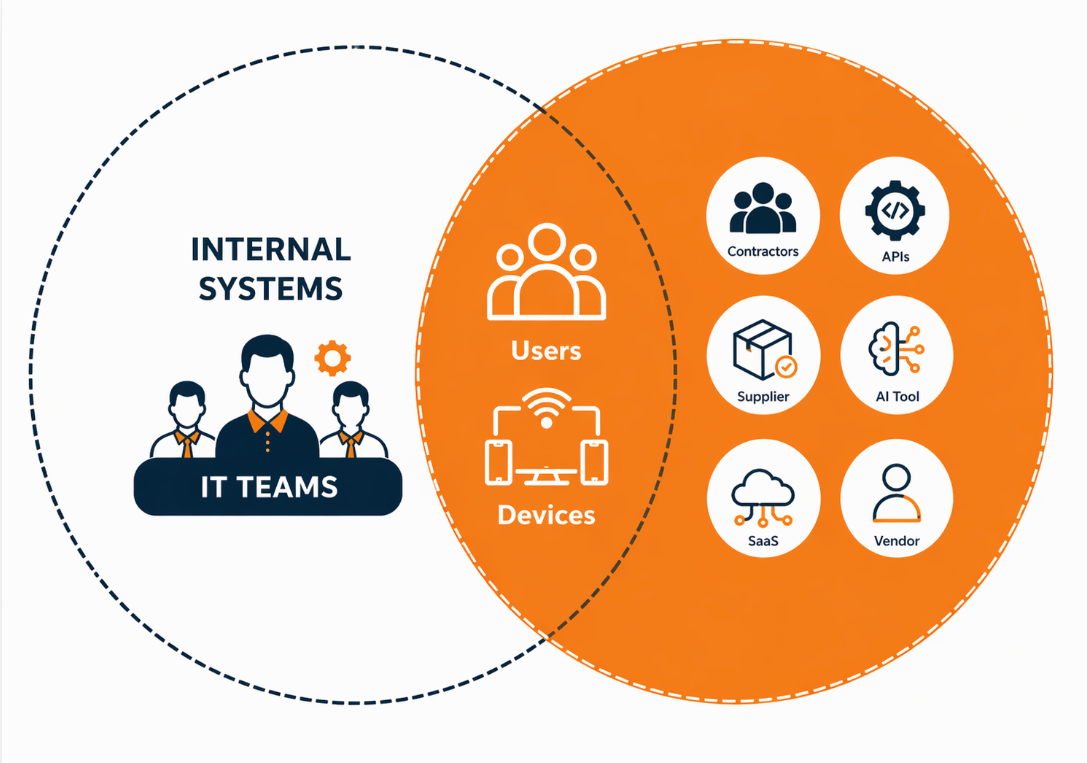
Third-party tools get connected during a product evaluation, a busy quarter, or a one-off project. Access gets granted. The project ends. The integration stays.
A vendor employee leaves their company. Their credentials are never revoked on your side. Those credentials surfaced on the dark web three months later. Someone logs in at 10 PM from a new device in Eastern Europe with perfectly valid credentials.
Your security team gets no alert. Because nothing looks wrong. The access is legitimate. The session is clean. The credentials are real.
How many of your current vendors have not enforced MFA? How many integrations in your environment were connected by a department and never reviewed by security? How many vendor accounts still have standing access for a project that ended six months ago?
Most organisations cannot answer any of those questions. Not because they are not trying. Because the tooling to answer them has not been part of the standard security stack.
This keeps getting framed as an IT problem. But IT does not have visibility over this either. Boards expect their teams to own third-party risk without giving them the tools to see it. That is not a security gap. It is a visibility gap. And attackers have been exploiting it consistently for two years running.
What real visibility actually looks like
Most security tools monitor what they already know about. Endpoints, known applications, and traffic within defined perimeters. Third-party SaaS connections live outside all of those boundaries.
Real visibility means knowing every external connection in your environment. Not just the ones IT approved last quarter. Every OAuth token, every vendor identity with standing access, every integration a department connected to and never told security about.
It means understanding what normal looks like for each of those connections. What time does this tool typically run? What data does it typically reach? What devices and locations does it connect from? That baseline is what we call the Pattern of Life. And it is what turns a suspicious login into an actionable signal before it becomes a breach.
When a vendor account that normally connects during business hours suddenly authenticates at 10 PM from a new Linux device in a country it has never been seen in before, that is not a breach happening inside your systems. It is a breach happening at your vendor. And without a behavioural baseline underneath every connection, you will never see it.
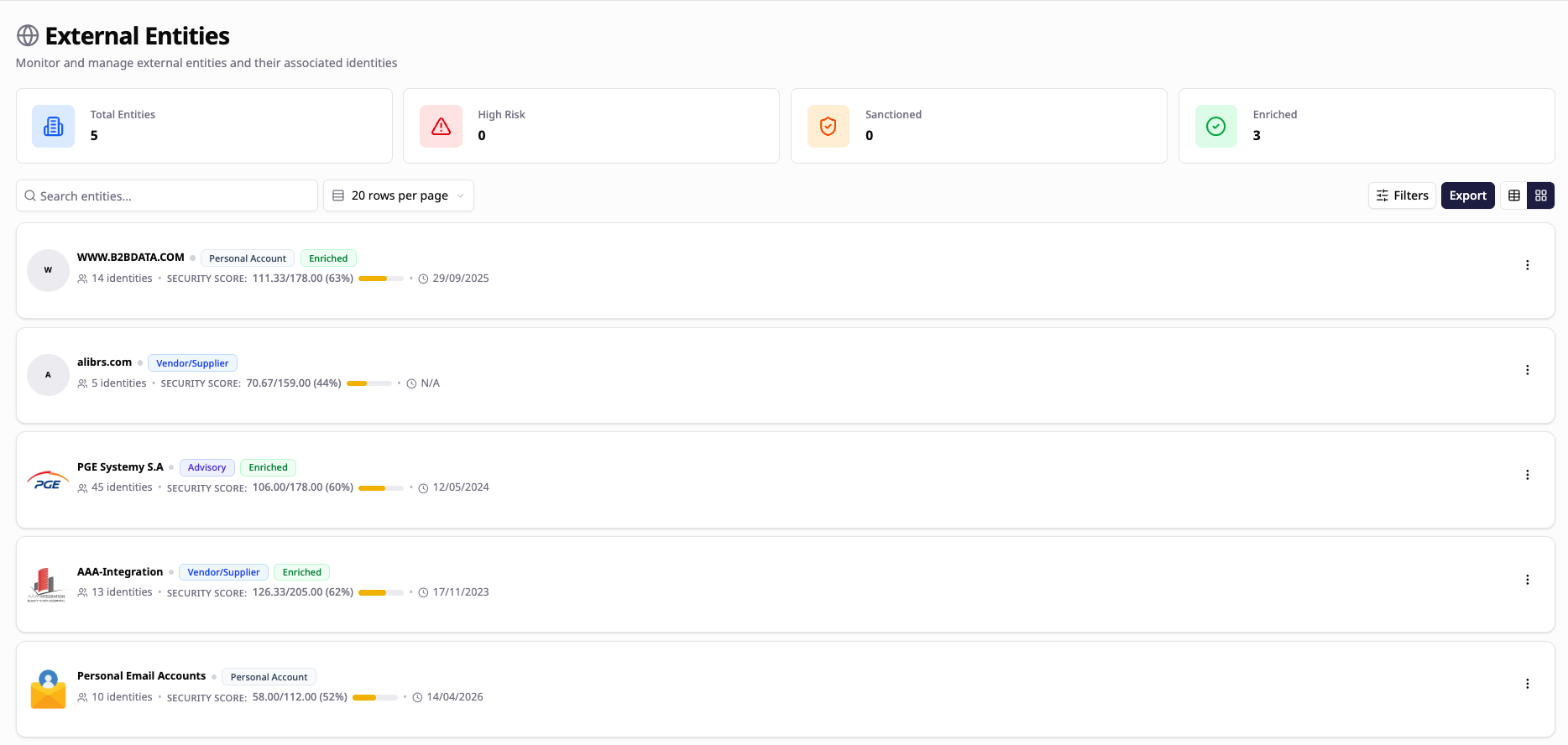
A single pane of glass across your entire third-party environment, every supplier, every partner, every SaaS or AI tool with access to your data, monitored continuously with behavioural context, is what separates organizations that catch this early from those that find out from a ransom note.
That is what FrontierZero does.
The question worth asking today

Every analytics platform, every outsourced support provider, every SaaS integration connected over the last three years is an external identity inside your environment. Most have never been reviewed. Some belong to people who no longer work at the vendor. A number of those vendors have never enforced MFA.
You do not have to be breached directly. You just have to be connected to something that is.
The organizations that come out worst from incidents like Vimeo are not the ones with the weakest security. They are the ones with the biggest blind spots.
If you want to know what is connected to your environment right now, we will show you in 15 minutes. No pitch. Just visibility.
🔍 Get your free External Connections Report: https://frontierzero.io/external-access-report/