Rockstar Breach Explained: 78.6 Million Records. Zero Alarms. One Unmonitored Vendor.
Rockstar wasn’t breached through their own systems. Attackers compromised a vendor, used legitimate access into Snowflake, and walked away with 78.6 million records, without triggering a single alert.
ShinyHunters, the group behind breaches at Ticketmaster, AT&T, and Microsoft, posted a message on their dark web site on April 11th: "Rockstar Games, your Snowflake instances were compromised thanks to Anodot.com. Pay or leak." The ransom deadline was yesterday, April 14th.
Rockstar confirmed it. 78.6 million records, tied to their Snowflake cloud environment. And Rockstar wasn't the only victim. At least a dozen companies were exposed through the same breach at Anodot, all facing extortion, all at risk of having their data published.
Here's what makes this worth understanding beyond the headline: Rockstar's own systems weren't breached. Attackers exploited a breach at Anodot, a SaaS platform used for cloud cost monitoring, to obtain authentication tokens, which then allowed them to access Rockstar's Snowflake instances without exploiting Snowflake's own security. The access looked completely legitimate. No alerts fired. No perimeter was crossed.
The hackers didn't break in. They logged in, using credentials that weren't theirs, through a connection that nobody was watching.
If you'd like to know which connections in your environment look like this right now, we can show you for free here.
A pattern that ran through all of 2025 and is continuing in 2026
If this feels familiar, it should. The Rockstar breach is the latest in a sequence that has now touched some of the most recognisable organisations in the world.
In June 2025, Qantas detected unusual activity on a third-party platform used by its contact centre. The breach affected up to 6 million customers. Qantas' own infrastructure was never touched. The attack lived entirely within a vendor's environment, one that had access to customer data Qantas was ultimately responsible for.
In August 2025, Jaguar Land Rover was hit. Three UK manufacturing plants were forced to shut down, and the disruption rippled through more than 5,000 British organisations. Production halted for five weeks. Estimated losses reached £1.9 billion. The most financially damaging cyber event in UK history. The entry point, again, was not JLR's own systems. (read more about it here)
Marks & Spencer lost roughly £300 million in operating profit and was forced to suspend online orders for 46 days after attackers used a far simpler method: they tricked a third-party provider into resetting an internal user's credentials. No firewall bypass. No zero-day exploit. Just a phone call to the wrong person, and a door that opened from the inside.
And last month, HackerOne, a company whose entire business model is finding security vulnerabilities before attackers do, sent breach notifications to its own employees. The breach stemmed from Navia Benefit Solutions, a third-party benefits administrator, where an attacker exploited a vulnerability and accessed sensitive data over a period of several weeks without detection. (read more about it here)
The through-line across all of these is not sophistication. It's invisibility. Attackers are consistently finding their way in through connections that organisations provisioned, forgot about, and stopped monitoring, and in most cases, the victim organisation had no visibility into what was happening until it was already over.
Why does this keep happening to organisations that are doing everything else right
This is the part that's genuinely uncomfortable to sit with.
Rockstar has a security team. Qantas completed an uplift of its third-party cyber risk governance processes in 2024. HackerOne literally runs a platform for finding vulnerabilities. M&S, JLR, these are not organisations that ignore security. And yet here we are.
The problem isn't diligence. It's structural.
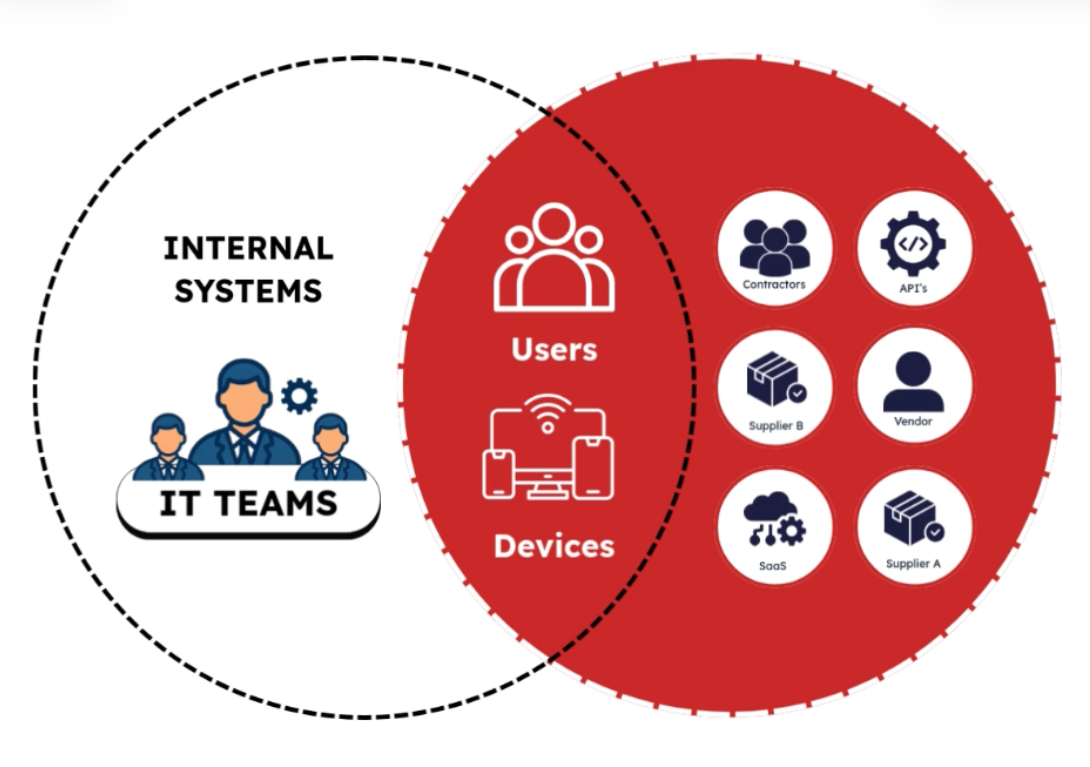
The tooling most organisations rely on was built for a world where the perimeter was the boundary. Protect the firewall, monitor the endpoints, and audit internal access. That model made sense when most of your data lived inside your own infrastructure. It doesn't reflect how organisations actually operate anymore.
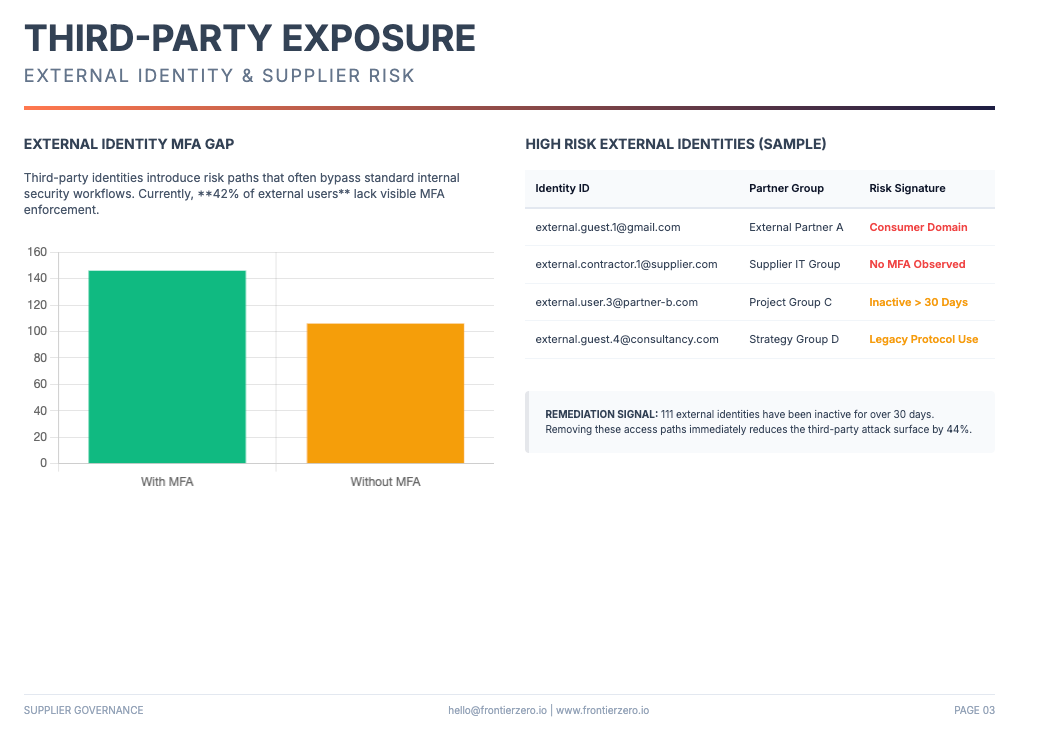
Today, the average enterprise has hundreds of SaaS integrations. Vendors with privileged access to internal systems. Contractors whose credentials were provisioned and never removed. Tools that were connected by one team and are now owned by nobody. Every one of these is an external connection, and most organisations have no consolidated view of what those connections are, what access they carry, or whether the associated identities are still legitimate.
Think about how Anodot ended up in Rockstar's environment. An engineering or finance team signs up for a cloud cost monitoring service. It's a reasonable tool that solves a real problem. Access gets provisioned to Snowflake. The integration goes live. Time passes, priorities shift, and that connection quietly becomes part of the background, active, trusted, and entirely unreviewed. Until ShinyHunters finds it.
That story is not unique to Rockstar. It is happening in your environment right now.
The layer most teams aren't watching
There's a dimension to this that rarely gets discussed in breach coverage, because it's harder to illustrate than a hacked login page or a phishing email.
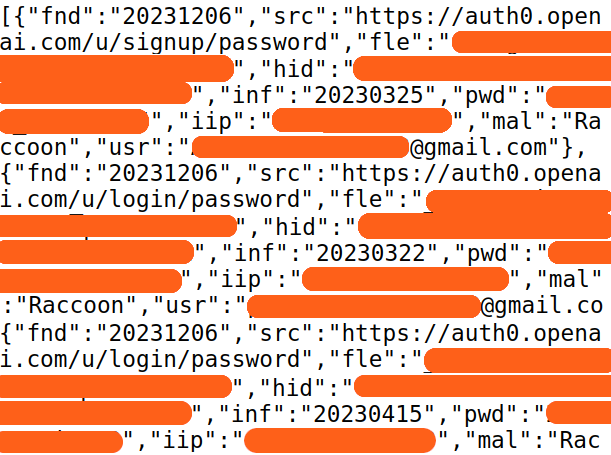
Breaches rarely begin at the moment of attack. Credentials are stolen weeks or months earlier through phishing campaigns, infostealer malware, or exposure in a previous unrelated breach, and then traded or held until the right target presents itself. By the time an attacker is moving through your environment, the original compromise may be months old and entirely cold.
This means that right now, without anything having gone visibly wrong, credentials associated with your vendors may already be circulating. A contractor who left six months ago may still have active access. A vendor that doesn't enforce MFA on accounts touching your systems may be one stolen password away from becoming your problem.
None of this is detectable through periodic audits or annual vendor questionnaires. It requires continuous visibility: knowing what's connected, knowing what normal behaviour looks like for each connection, and being able to detect when something deviates from that baseline before data starts moving.
When an integration that normally reads configuration data begins pulling records at volume, that's a signal. When an account provisioned for a narrow purpose starts acting outside its expected pattern, that's a signal. Catching these early, before exfiltration, before the ransom note, is where breaches can still be stopped.
The organisations that handled the incidents above the worst were the ones that found out last. Not because their security teams were failing, but because they had no mechanism to see what was happening in the connections around them.
The question that matters
There's one question we think every security leader should be able to answer right now, without pulling a report or scheduling a vendor review:
If one of our vendors was compromised tonight, how exposed are we?
Not in general terms. Specifically. Which vendors have access to which systems? Is that access still active and justified? Are any associated credentials already exposed? Is anything in your external connection layer behaving abnormally right now?
Most teams cannot answer this fully. Not because they haven't tried, but because the visibility to answer it has never existed in one place.
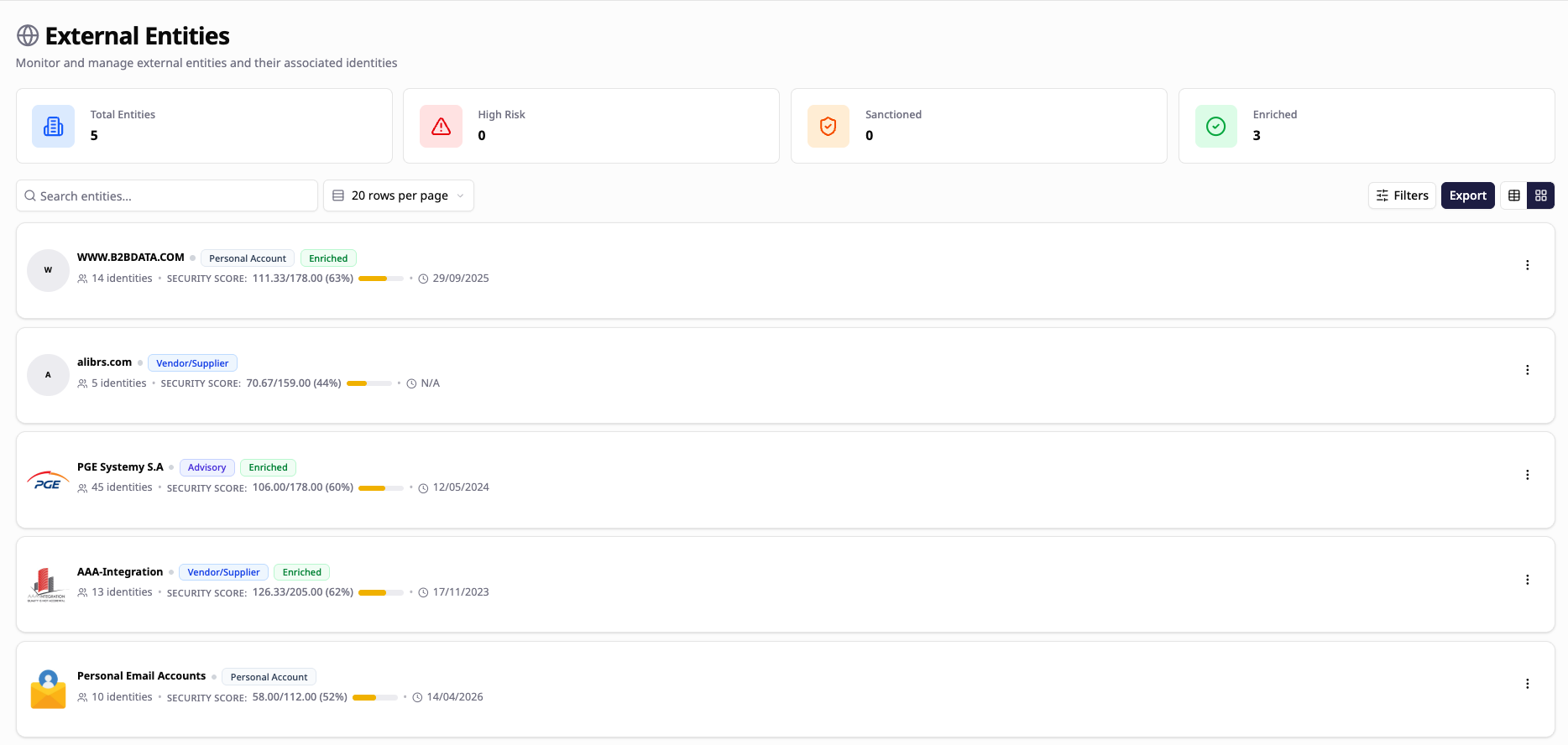
That's the gap FrontierZero was built to close.
We map every external connection in your environment: vendors, contractors, SaaS integrations, with real context around what access each entity has, whether it remains active, and whether associated identities are already compromised. Pattern-of-life monitoring runs underneath all of it, surfacing deviations before they become incidents.
No heavy onboarding. No internal lift.
If you'd like to see what's actually connected in your environment, we'll produce a free External Connections Report scoped to your organisation.