The Third-Party Breach List Keeps Growing. Vimeo is the latest to join.
Vimeo was breached through Anodot, a third-party analytics tool. So was Rockstar Games. Same vendor, same month. This is no longer a pattern. It's the playbook.
Vimeo was breached through Anodot, a third-party analytics tool. So was Rockstar Games. Same vendor, same month. This is no longer a pattern. It's the playbook.

An AI tool with OAuth access. A trusted session. No alerts. The Vercel breach shows how Shadow AI is becoming the easiest way in.
Rockstar wasn’t breached through their own systems. Attackers compromised a vendor, used legitimate access into Snowflake, and walked away with 78.6 million records, without triggering a single alert.

HackerOne wasn’t breached directly. A supplier was. One vulnerability exposed millions across multiple organisations. This is how modern attacks really happen, and why most companies still don’t see the risk.

Attackers didn’t breach Crunchyroll’s systems, they logged in through a compromised vendor account. The incident highlights a growing risk: third-party access across SaaS environments.

A recent campaign linked to North Korea’s Lazarus Group targeted organizations in the Middle East using Medusa ransomware. The attack highlights how modern ransomware operations work—and why identity and SaaS visibility are becoming critical for security teams.

A breach at Conduent exposed the data of 25 million Americans after attackers remained inside the vendor’s systems for three months.
For nearly a decade, a malicious Chrome extension quietly collected session cookies and authenticated access from real users inside real companies. The story behind ShadyPanda highlights a growing blind spot in modern security: what happens inside authenticated SaaS sessions.

AI tools are spreading across organizations faster than most security teams can track. Each OAuth login or SaaS integration can quietly create persistent access to company data, often without centralized visibility.
Microsoft gives strong identity visibility, but only inside Microsoft. This explains where today’s SaaS attacks actually start.
In December, Nissan lost customer data — even though its own systems weren’t hacked. The problem came from an external platform with standing access. Read how this happened, why it keeps repeating, and what security teams should change.

Google-native companies tend to move quickly. Their teams adopt new tools early, automate workflows efficiently, and rely on the browser as the central work environment. This speed is rarely a “security issue”; it’s a modern pattern that emerges naturally when companies build on a flexible, cloud-first platform like Google
Roundtables
Our closed-door CISO roundtable in Dubai highlighted a major shift: the perimeter is gone, and real-time identity behavior now defines effective security.

SaaS Security
Most breaches slip through not for lack of alerts, but for lack of context. Context-based security brings clarity to chaos — helping teams focus on what’s real.

Cybersecurity
Jaguar Land Rover lost millions when one contractor account went unchecked. This wasn’t a system failure; it was a visibility failure. Here’s what every CISO can learn about identity risk and supply chain trust.
SaaS Security
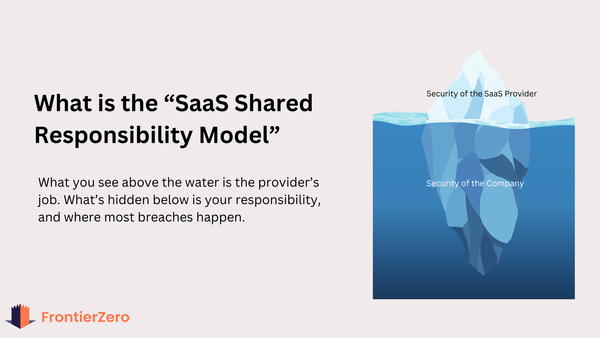
SaaS providers secure the platform. You’re responsible for everything inside it: users, vendors, permissions, and risk. This blog breaks down where responsibility lies, what’s commonly missed, and how CISOs can prevent the most common SaaS breaches.
SaaS Security
Privilege creep happens when users accumulate admin access over time. In SaaS environments, this creates invisible risk: inactive accounts, missing MFA, and external admins hackers love to exploit. Here's how to find and fix it before it’s too late.

Shadow IT
Discover the 5 departments most likely to introduce it into your SaaS environment.

Boardroom
Insights from the 2025 IBM Cost of a Data Breach Report

SaaS Security
The latest IBM Cost of a Data Breach Report just dropped—and while headlines focus on global averages, the real insights for CISOs lie deeper. From regional cost surges to the hidden price of Shadow AI, here are five takeaways you can use to protect your organization in 2026 and beyond.
MFA
MFA gaps aren’t just an IT problem—they’re a boardroom risk. Learn how to spot exposed users, admins, and apps in minutes, not months.

SSPM
SaaS tools are the new business layer—but they’ve created a visibility gap security teams can’t ignore. This guide explains what SSPM is, why it matters, and how FrontierZero brings identity and context together to reduce risk where it matters most.
SaaS Security
Orphaned SaaS accounts are the invisible risk lurking in every organization. Learn how ex-employees, contractors, and automations keep access long after offboarding — and why modern security teams are shifting to identity + context to shut it down.
ITDR
SaaS has changed the identity perimeter. In this guide, we break down what ITDR means, why legacy tools miss SaaS threats, and how to catch ghost access.