Zara Breach Explained: Here's The Hacker Playbook for 2026
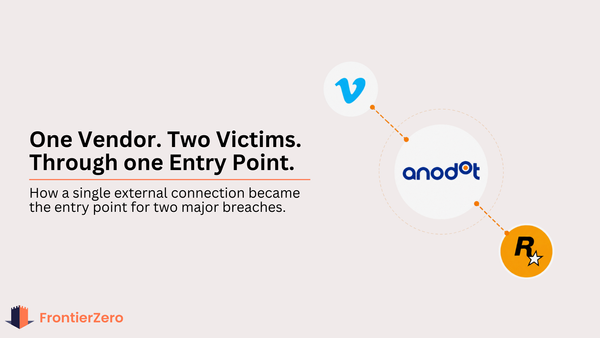
ShinyHunters didn't hack Zara, Vimeo, and Rockstar separately. They compromised one vendor and got all three. Here's the exact playbook they used.
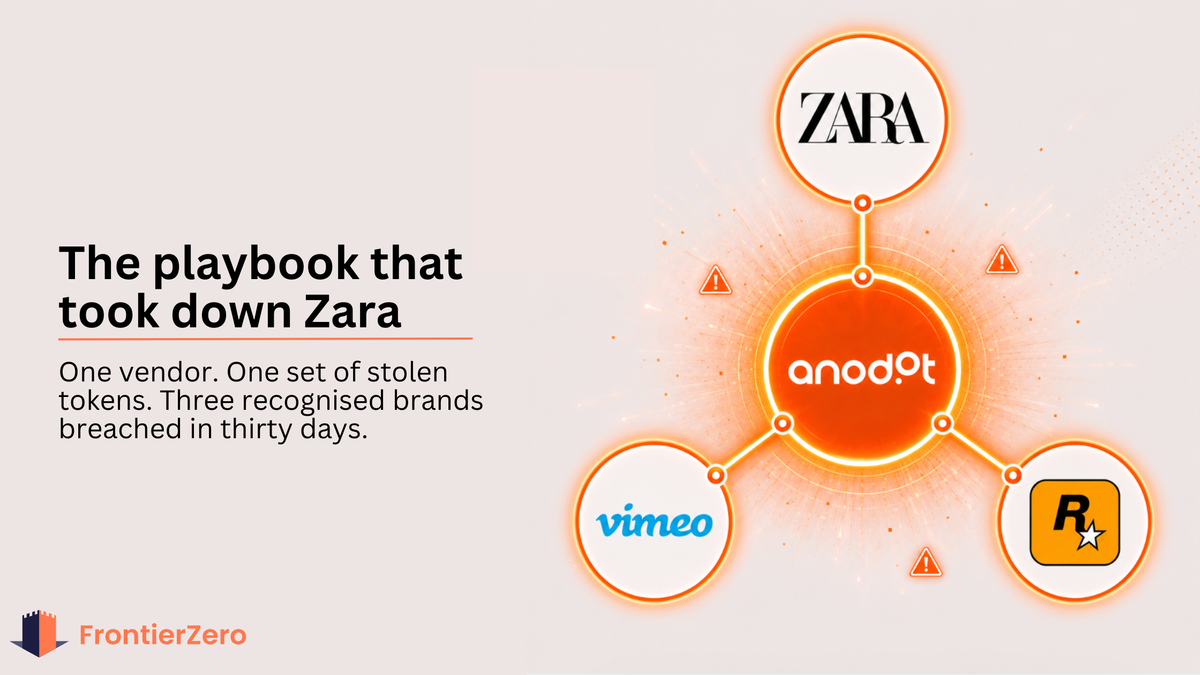
In April 2026, ShinyHunters breached three of the world's most recognizable brands in thirty days.
Zara. Vimeo. Rockstar Games.
They did not use three separate attacks. They did not find three separate vulnerabilities. They used one playbook, executed it against one vendor, and everything connected to that vendor came with it.
This is exactly how they did it.
Step 1: Don't target the company. Target the vendor everyone uses.

ShinyHunters did not start with Zara. They started with Anodot.
Anodot is a cloud analytics platform connected to Snowflake and BigQuery environments across dozens of large enterprises simultaneously. Trusted. Persistent. Almost never reviewed by security teams.
To find it as a target, you only need to ask one question: which vendor has authenticated access to the most enterprise environments at once?
Analytics platforms. Monitoring tools. BI connectors. Compromise one, and you do not get one victim. You get everyone connected to it.
This is the shift. Attackers are not looking for the hardest target anymore. They are looking for the most connected vendor.
Anodot was that vendor.
Step 2: Steal the tokens. Inherit the access.
Anodot authenticates into customer environments using API tokens. Persistent. Legitimate. Designed for convenience.
When stolen, they are completely indistinguishable from legitimate access.
ShinyHunters compromised Anodot's authentication layer and extracted those tokens. One set of credentials. Dozens of environments. All open simultaneously.
From Inditex's BigQuery environment alone, they pulled 197,400 customer records. Email addresses, order IDs, purchase histories, support ticket content. From Rockstar, 78.6 million records. From Vimeo, user and customer data were published in full after they refused to pay.
Zero alerts across all three. The tokens were valid. The sessions were clean.
The access looked completely legitimate. Because it was.
Step 3: Exploit the door nobody remembered to close.
Here is what almost every news outlet missed in Inditex's statement.
They did not call Anodot a current provider. They called them a former provider.
The relationship had ended. The contract was closed. But the tokens Anodot held to access Inditex's BigQuery environment had never been revoked. Still active. Still valid. Waiting for whoever found them next.
This is not a Zara problem. This is the norm.
Think about how third-party access accumulates. A marketing team connects an analytics tool during a campaign. A finance team integrates a monitoring platform for a quarterly review. An IT team grants a vendor Snowflake access for a one-off project. Each one creates a persistent identity inside your environment with standing access to sensitive data.
When the project ends, the access rarely goes with it. Nobody owns it. Nobody tracks it. Nobody revokes it.
ShinyHunters did not breach Inditex. They found the token Inditex had forgotten existed.
Step 4: Set the deadline. Publish when nobody pays.
This is where the operation becomes a business.
ShinyHunters listed all three companies on their Tor leak site simultaneously. They named Anodot publicly as the compromised vendor, something Inditex has still not confirmed in its own communications. They issued pay-or-leak deadlines with specific dates, creating urgency and public pressure at the same time.
Zara's deadline was April 21st. They did not engage. ShinyHunters published the full archive the following morning.
Have I Been Pwned confirmed the scope on May 8th. 197,400 people notified. The data was exactly what ShinyHunters had claimed all along.
The entire operation, from first compromise to published leak, took less than two weeks per target. No zero-day exploits. No sophisticated social engineering. No direct interaction with Zara, Vimeo, or Rockstar's own infrastructure at any point in the chain.
One vendor. Stolen tokens. Doors that were never closed.
And three companies that will spend years managing the fallout from an attack that never touched their systems.
organizations
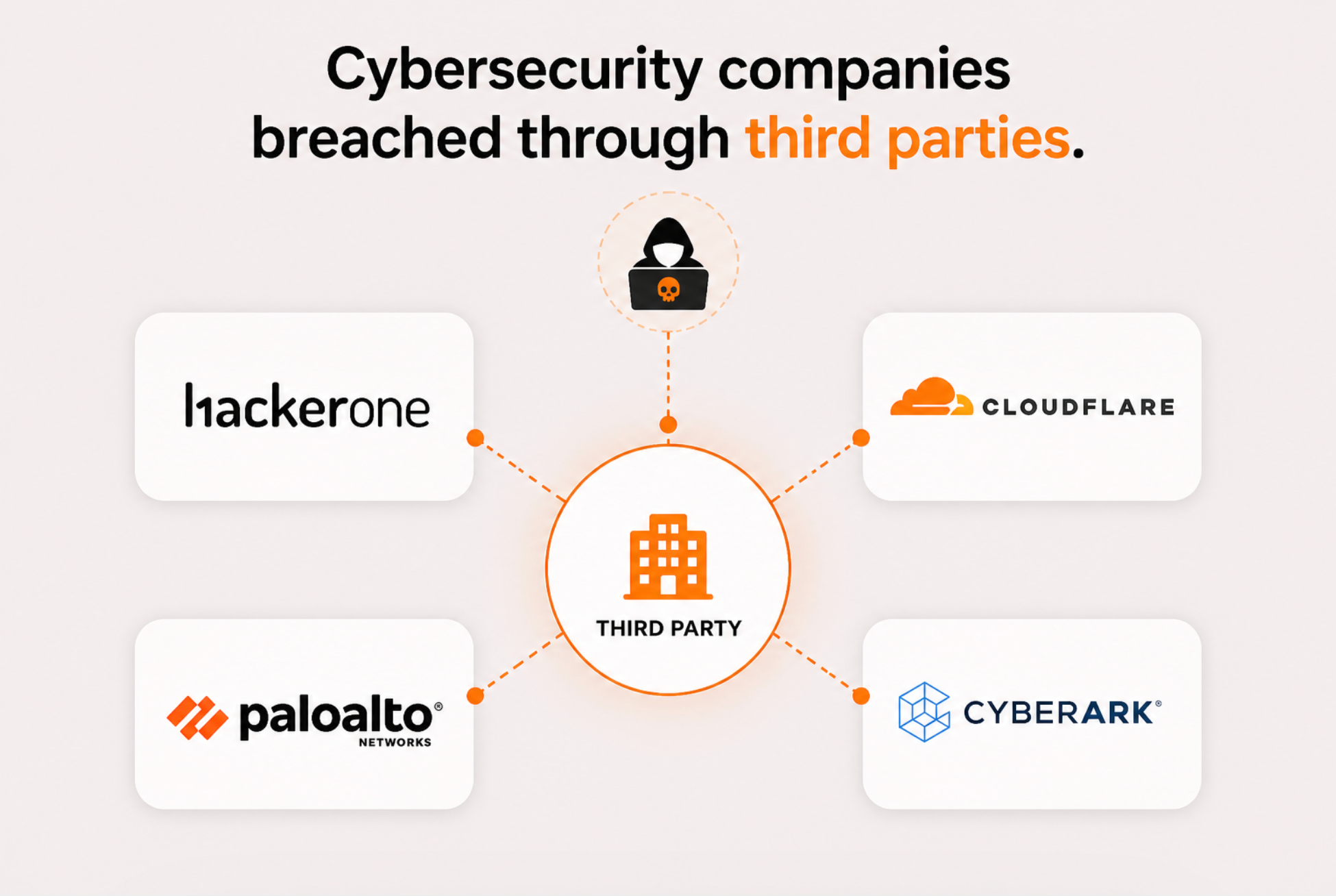
In 2025, one chatbot provider took down Cloudflare, Palo Alto Networks, CyberArk, and twenty more simultaneously. The same hotel software hit Marriott, Hilton, Hyatt, and Wyndham in one incident. JLR, Qantas, Workday, all through supply chains rather than direct attacks.
These are not small companies with immature security programmes. These are the organizations that write the playbooks everyone else follows. And they all had the same blind spot.
One vendor. Multiple victims. Every time.
The former vendor problem makes it worse. Every organization that has ended a third-party relationship without revoking every token and credential that the vendor held is carrying a risk right now that they cannot see or quantify.
Can you answer these questions today?
- Which former vendors still have active tokens in your environment?
- Which integrations were connected by a department two years ago and never reviewed?
- Which service accounts belong to companies you no longer work with?
If you cannot, you are carrying a massive risk at the moment.
the
Two things most security programmes do not have.
The first is complete visibility. A real-time map of every external connection into your environment, not just current vendors. Every token, every OAuth connection, every service account with standing access, including ones from vendors you stopped working with last year. You cannot revoke what you cannot see. And you cannot monitor what you do not know exists.
The second is behavioural context. Knowing a connection exists is the starting point. Understanding what normal looks like for that connection is what makes anomalies visible. What time does this integration typically authenticate? What volume of data does it query? What devices and locations does it connect from?
That baseline is what we call the Pattern of Life.
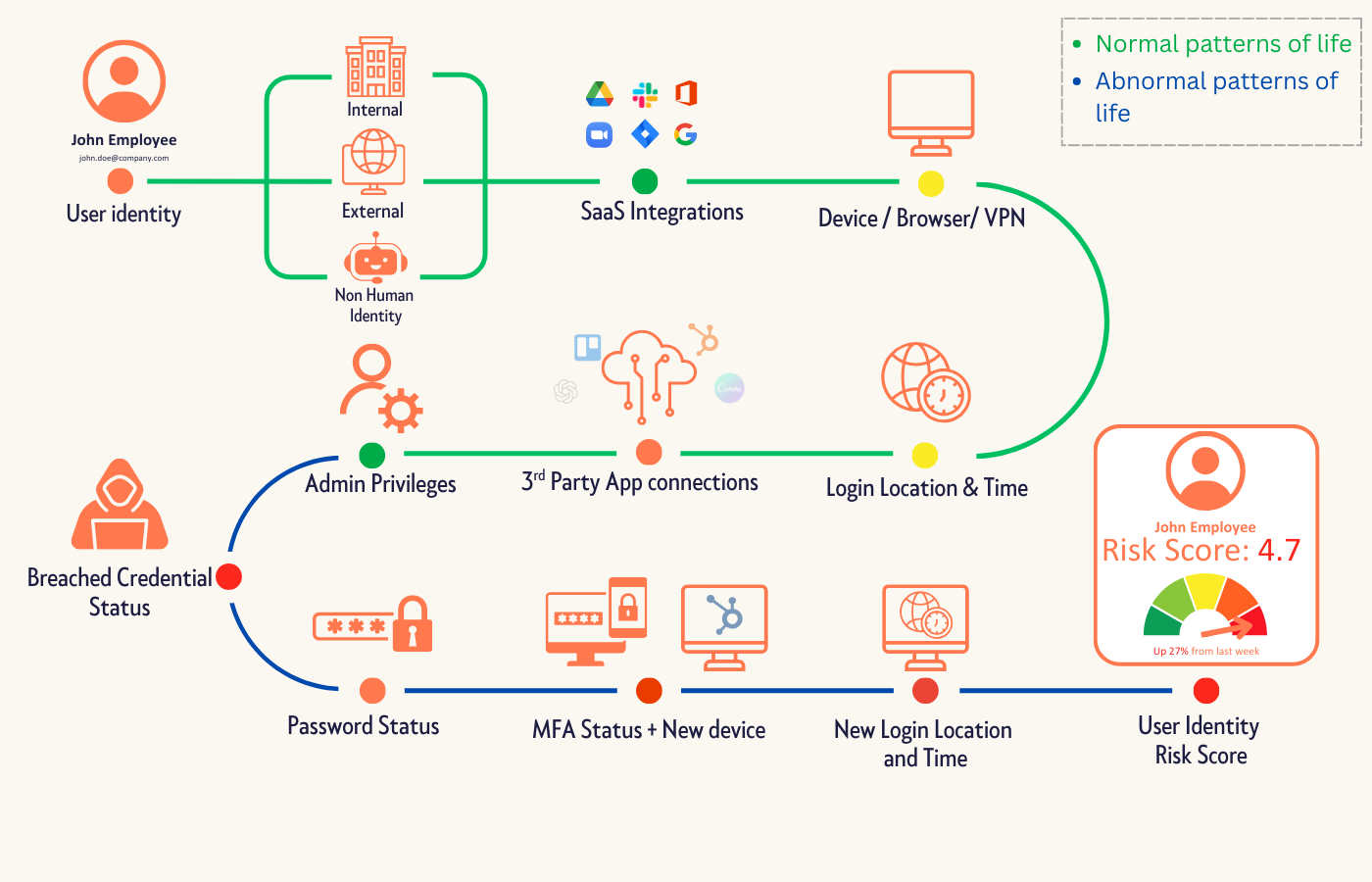
Here is what that looks like in practice. A vendor account logs into an analytics platform at 11 PM. New device. New region. No VPN. And you know from threat intelligence that their credentials have been circulating on the dark web for three weeks. Without a behavioural baseline, that login is invisible. Against one, it is an alert you can act on before a single record leaves your environment.
That is the difference between catching it and reading about it on BleepingComputer.
Most organizations are flying blind on this. Not because the problem is unsolvable. Because the tooling to solve it has not been part of the standard security stack until now.
A single pane of glass across your entire third-party environment, every current vendor, every former vendor, every token and OAuth connection, monitored continuously with behavioural context underneath. That is what separates organizations that catch this early from those that find out when Have I Been Pwned sends the notification.
That is what FrontierZero does.
The question worth sitting with
ShinyHunters did not need to be clever. They found a shared vendor, stole some tokens, and walked through doors that organizations had forgotten to close.
How many of those doors exist in your environment right now?
And if one of them opened tonight, would anyone know?
We will show you in 15 minutes. Better to be safe than sorry.
🔍 Get your free External Connections Report: https://frontierzero.io/external-access-report/